Want to learn some WordPress security vulnerabilities?
The web is a dangerous place because behind every website are users, resources, and data that criminals want to exploit. It is dangerous because criminals only have to be lucky once, but you, as a website owner, have to do the right thing every day to keep your site safe.

WordPress is a secure content management system with strong defenses, but it needs help. And to help, you need to be aware of the risks faced by your WordPress site. Once you understand the risks, it is easier to understand the part you play in keeping your site, its users, and its data out of the hands of criminals.
1. Brute Force And Dictionary Attacks – WordPress Security Vulnerabilities
Your WordPress site knows who you are because you logged in with a username and password. If an attacker guesses the right username and password, your site will give them the same access. If they guess the credentials for a user with administrator privileges, they have complete control.
Brute force attacks — and dictionary attacks that use lists of common passwords — are the least sophisticated and most common attack against WordPress sites. They work because people choose passwords that are easy to guess.
2. Cross-Site Scripting Attacks – WordPress Security Vulnerabilities
WordPress themes use JavaScript, a programming language that runs in web browsers, to provide interactivity and other enhancements. The JavaScript files are provided to the browser by WordPress when pages are loaded. But sometimes a programming error allows an attacker to add their own JavaScript to the page.
Web browsers adhere to the Single-origin Policy. They trust scripts that originate from the same place as the web page. If an attacker can inject content into the page, then the browser trusts it and executes it. The code has access to all of the data related to the page, including session cookies and data entered into forms, such as credit card numbers. In a cross-site scripting attack, malicious code sends that data to a server under the control of the attacker.
Malicious JavaScript can be injected into WordPress pages through several vectors. If WordPress or a plugin adds a user input element to a page, such as a comment form, but fails to properly sanitize the input, then the code in the comment will be run in the browsers of future visitors to the page.
One of the most pernicious XSS vectors is the supply-chain attack. Instead of attacking individual sites, bad actors attack the JavaScript libraries or plugins that WordPress sites use. When code is injected into a popular JavaScript library or plugin which is installed on WordPress sites, it will be served on the WordPress sites pages and run in browsers.
Typically, attackers inject a small piece of code into a popular library or plugin. That code then downloads a malicious payload and injects it into WordPress pages. In recent months, the MageCart credit card scraper has infected dozens of eCommerce sites using supply-chain attacks. In 2017, many popular WordPress plugins were acquired by a bad actor, who added malware code to them. In that series of attacks, the goal was spamming, but the same technique is used for XSS attacks.
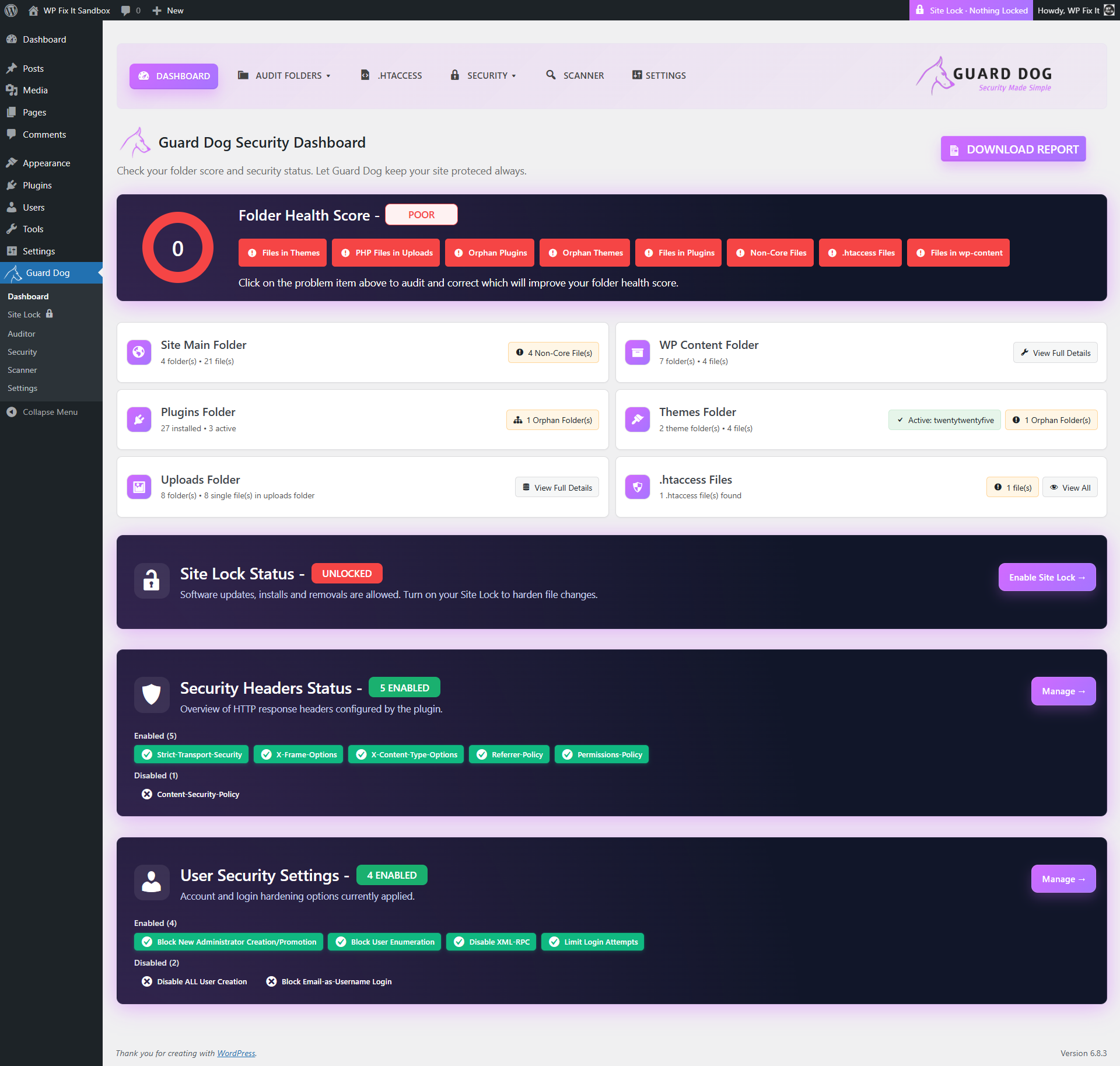
WordPress has defenses against cross-site scripting attacks: code entered into user input boxes is sanitized to render it inert. Browsers also have mechanisms to stop XSS attacks from running malicious code, including Content Security Policy, which is used to whitelist code the site owner wants to run. There is an excellent plugin for implementing Content Security Policies on WordPress stores.
However, developers, often plugin developers, make mistakes that cause vulnerabilities that criminals are only too happy to exploit.
3. Server Hosting Vulnerabilities – WordPress Security Vulnerabilities
A WordPress site is the tip of an iceberg that also includes a web server, a PHP interpreter, an operating system, a database, and lots of utility software. A vulnerability in any of that software could be used to compromise the server and, therefore, any WordPress site it hosts.
The Spectre and Meltdown vulnerabilities are a prime example of a critical vulnerability in the hardware of modern servers. Spectre and Meltdown exploit a vulnerability in performance optimizations in the processors (CPUs) used on most enterprise servers. They can be exploited by a user who can run code on a server to extract data owned by other users and by the operating system itself, including private keys and other sensitive information. Spectre and Meltdown are particularly salient to users of WordPress shared hosting and cloud hosting, which host many users, including potentially malicious users, on the same server.
Responsible WordPress hosting providers have patched operating systems and server firmware to prevent bad actors from exploiting these vulnerabilities, but it’s an ongoing problem that WordPress users should be aware of.
4. Malware – WordPress Security Vulnerabilities
Malware is not a vulnerability, but criminals often exploit vulnerabilities so that they can install malware on a WordPress site. There are many different types of malware, including ransomware, cryptojacking scripts that mine digital currencies, SEO malware, and code whose job it to infect the devices of your users with other malware.
Keeping WordPress Sites Safe – WordPress Security Vulnerabilities
As WordPress site owners, your job is to make life as hard as possible for criminals. If you aren’t a developer or a technical expert, that means following four basic rules:
- Choose good passwords — If every user on your site chooses a long and hard-to-guess password, no one will be able to guess it. If you can’t trust everyone to choose a secure password (and you probably can’t), use a two-factor authentication plugin.
- Update frequently — Updates fix mistakes that cause vulnerabilities. Your site is more likely to be hacked if you don’t update WordPress and plugins when new versions are available.
- Choose your hosting wisely — You have to trust that your WordPress hosting provider is as careful as you are about security. That isn’t always the case. Look at reviews and the hosting provider’s reputation for security before you decide to host your site with them.
- Don’t help the hackers — Get your plugins and themes from reputable sources like WordPress.org. Don’t be tempted to install pirate premium themes and plugins; they are often infected with malware.
By following these four simple security best practices, you make life harder for criminals who want to exploit your site and its users.